From Prototype to Enterprise-Ready: A macOS Security Agent That Actually Ships
a US-based
Our client is a US-based cybersecurity software company operating in the endpoint device compliance space. They build SaaS products that continuously monitor managed devices and report compliance status to a centralized portal — a capability that sits at the core of their enterprise value proposition. They had a working agent. What they didn't have was a version they could actually ship to customers.
1. Requirement
1.1. Purpose
The client's agent worked in controlled conditions but failed in production. The engagement had a single, clear mandate: close the gap between a functional prototype and a product enterprise customers could install, trust, and never think about again. This meant resolving deep stability failures, achieving full compliance with Apple's platform security model, and leaving the client with a release pipeline they could run independently - not a one-time delivery they'd be dependent on us to repeat.
1.2. Detail Requirement
Functional requirements
- Persistent background operation: The agent must survive device reboots and user session changes without any manual intervention or monitoring.
- Reliable portal reporting: Continuous, uninterrupted compliance status reporting to the client's centralized cloud portal.
- Zero-friction installation: End-users install the agent without encountering any OS-level security prompts or warnings.
Technical & integration requirements
- Platform security compliance: Full conformance with Apple's notarization and runtime hardening requirements - not as a workaround, but correctly by design.
- Automated build pipeline: A repeatable, scriptable process for producing signed, distributable installers - reducing future releases to a single command.
- Credential sovereignty: A workflow architecture that keeps the client's Apple Developer assets entirely under their own control at every step.
Compliance requirements
- Full adherence to Apple Gatekeeper and notarization standards - non-negotiable for any enterprise macOS distribution.
2. Customer Problems
Agent fails in the real world: The agent ran fine in interactive mode but broke as a system daemon. In practice, this meant the product could not reliably do the one thing it existed to do - an existential problem for an endpoint compliance tool.
Product is undistributable: Without proper code signing and notarization, macOS prevented installation entirely. Enterprise customers couldn't even run the installer - making the product commercially blocked regardless of its functionality.
Every release is a liability: Each update required fragile, manual packaging steps. Slow to execute, easy to break, and impossible to hand off - the release process was becoming a ceiling on the product's growth.
1. Programming Language
- Python
2. Framework
- PyInstaller
- Launchd
3. Third Party
- Apple Hardened Runtime
- Codesign
- Notarytool
- Pkgbuild
4. Database
1. Challenge
The cybersecurity domain demands a higher bar on two fronts that cannot be traded off against each other:
- Apple Platform Compliance: The agent had to pass macOS Gatekeeper and notarization checks without exception - no user-facing security prompts, no workarounds. This required rebuilding the executable correctly under Apple's Hardened Runtime, not patching around it.
- Credential Sovereignty: The client's Apple Developer private keys, certificates, and credentials could never leave their own infrastructure at any point in the process. Any workflow that required BeevR to hold or access these materials was categorically off the table.
2. How to resolve these challenges
Fix the root cause, not the symptom: Background daemons fail for specific, diagnosable reasons - not random instability. We went to the architecture level to understand exactly why the agent broke in a daemon context, and redesigned its execution model accordingly. Stability came from correctness, not from patching around the problem.
Security constraint built into delivery, not bolted on: The credential security requirement shaped the entire workflow from day one. BeevR guides the process; the client controls the keys. Every signing and notarization step was designed around this constraint - protecting both parties without introducing friction or delay.
Make the client self-sufficient, not dependent: The most important deliverable wasn't the installer - it was the pipeline to produce future ones. A good engagement ends with the client needing us less, not more.
Result: The agent is live and fully operational in production. It installs silently via a signed and notarized installer, runs persistently through reboots and user session changes, and reports continuously to the client's portal - with no security warnings, no manual intervention, and no dependency on BeevR to maintain it.
Delivered at fixed-price with zero scope creep. The client now owns a self-sufficient release pipeline: future versions are signed, notarized, and ready to distribute via a single command.
Other Works
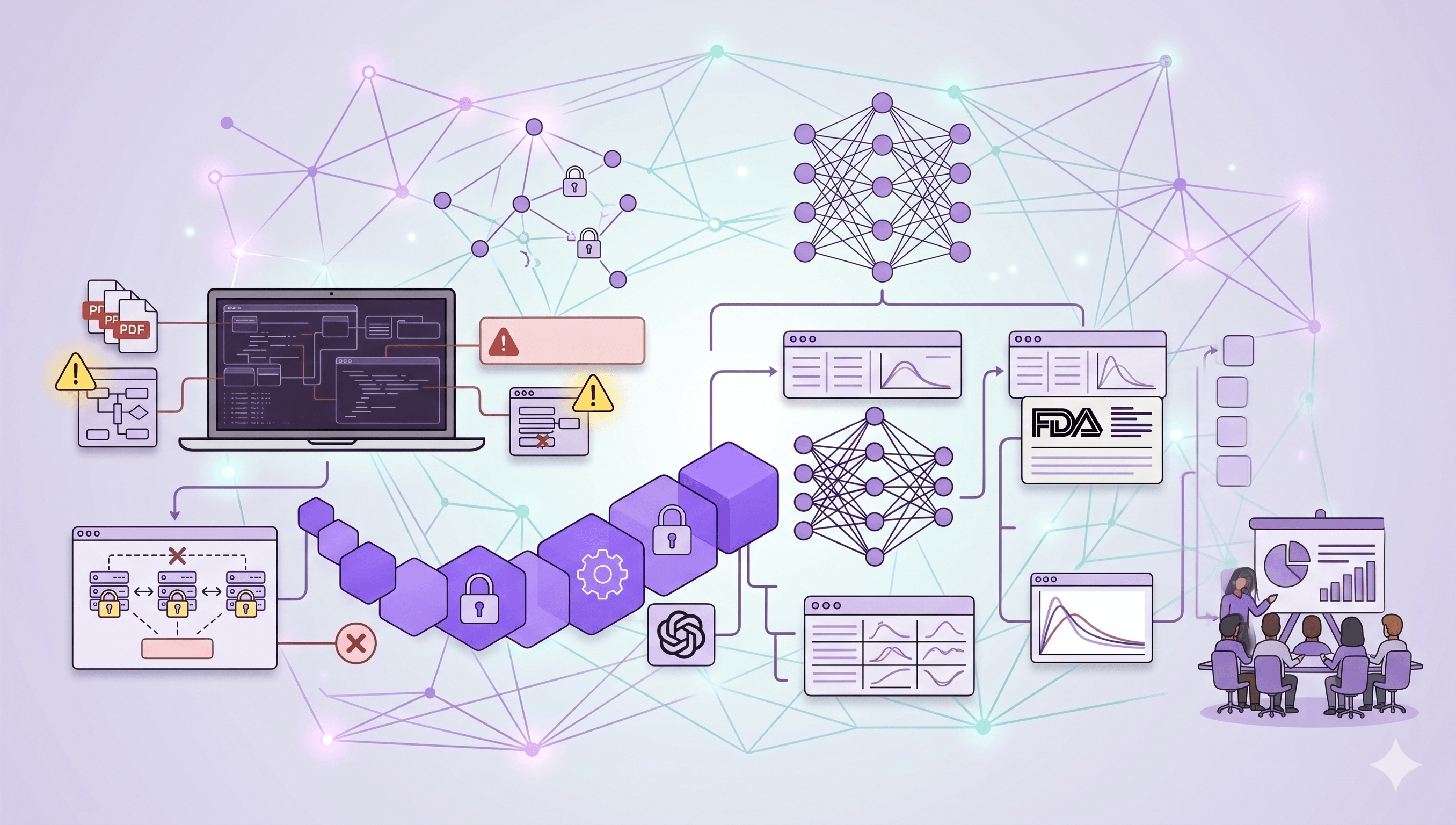
Bioequivalence AI Platform — From Clinical PDFs to Regulatory-Grade Assessment
An enterprise-grade bioequivalence AI platform delivering FDA-aligned assessments from unstructured clinical data - production-ready, fully client-owned.
From Reactive to Predictive - Revolutionizing US B2B Services
Revolutionizing US B2B Services from Reactive to Predictive using AI/ML and Custom ERP; achieving 15% cost savings and 30% process optimization.

Optimizing Manufacturing Assembly with Pick-to-Light
A software solution that transforms manual parts-picking into a fast, accurate, and efficient process for modern manufacturing assembly lines.